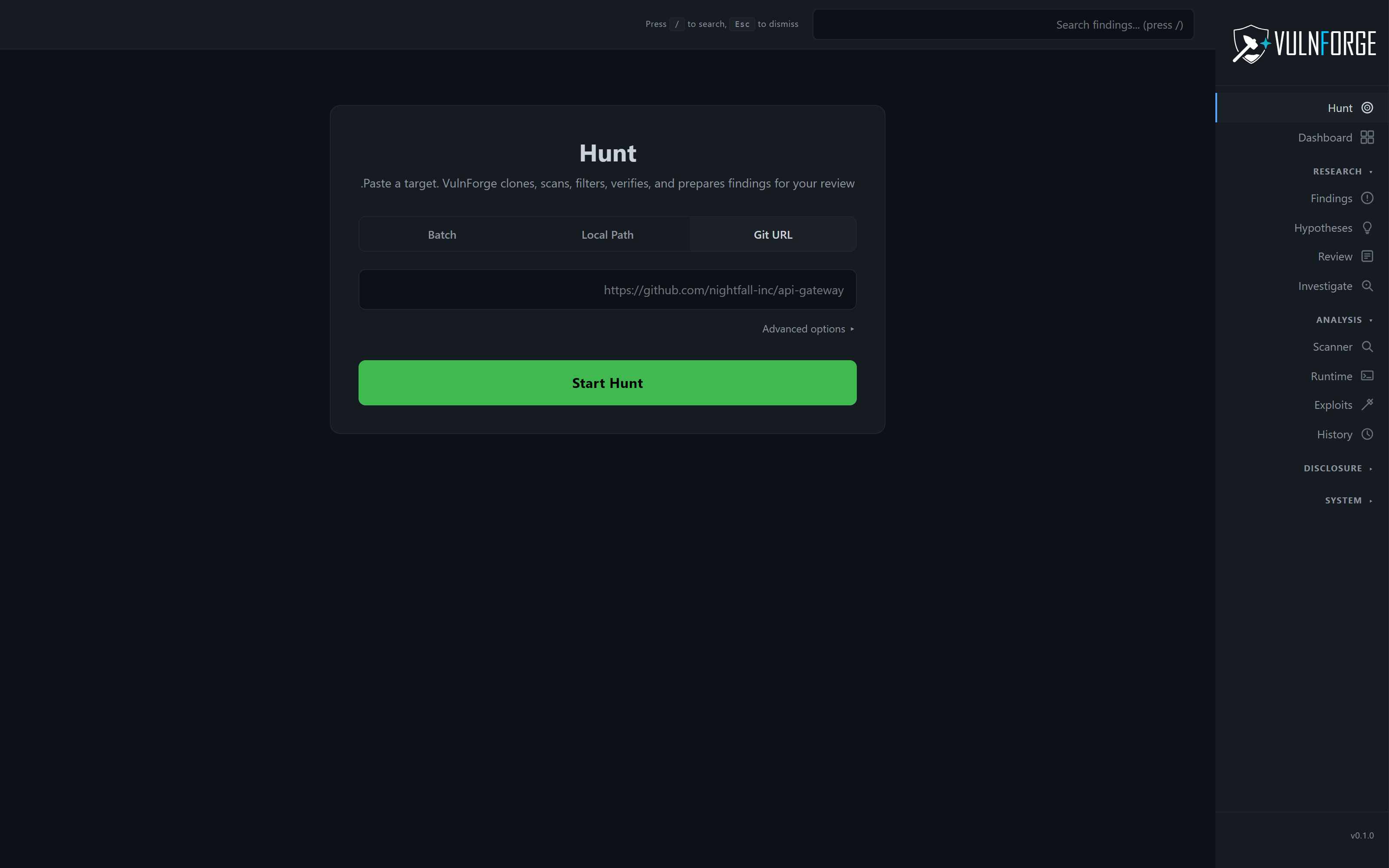
01 · Paste a URL → reviewed finding
Core pipeline
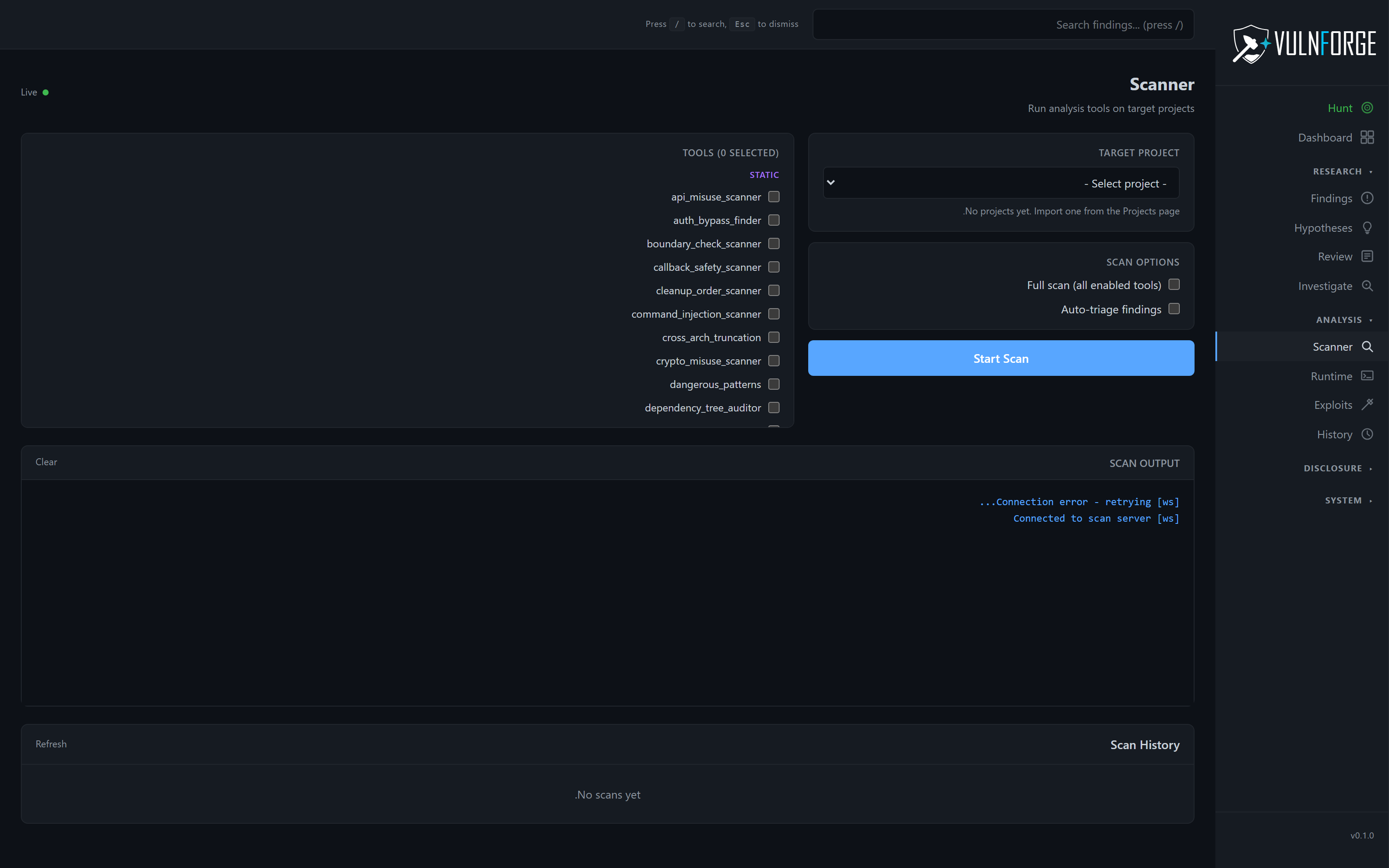
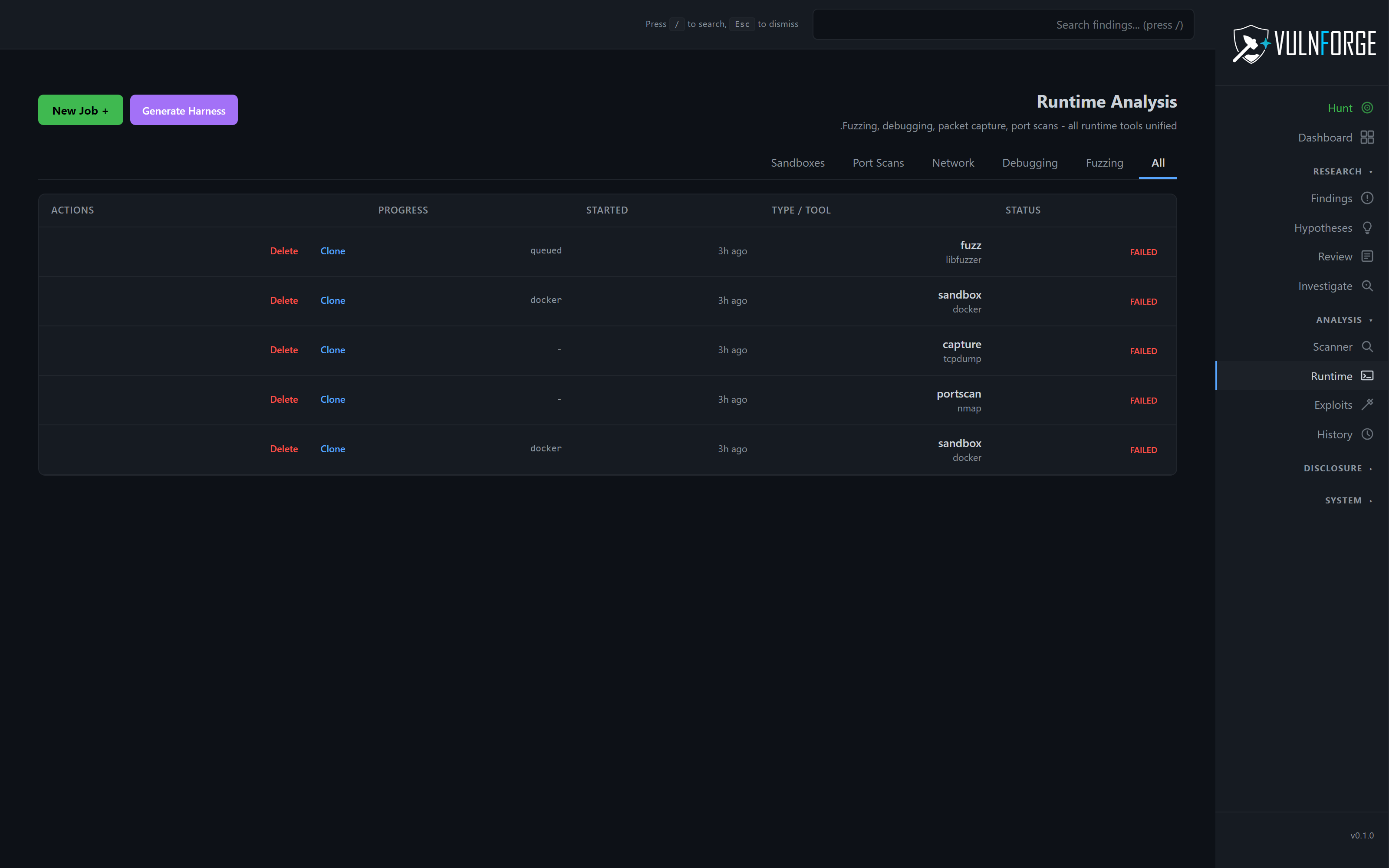
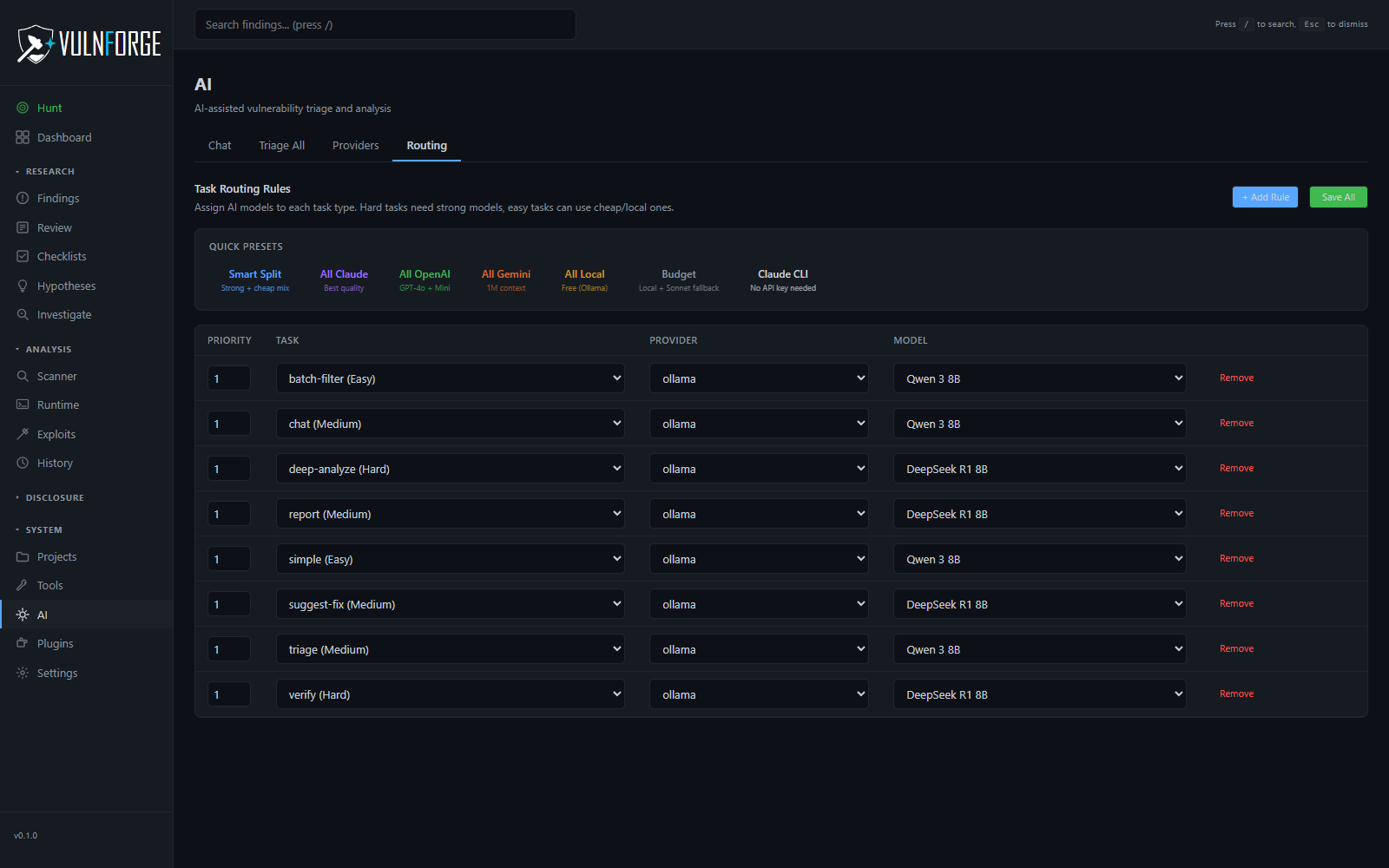
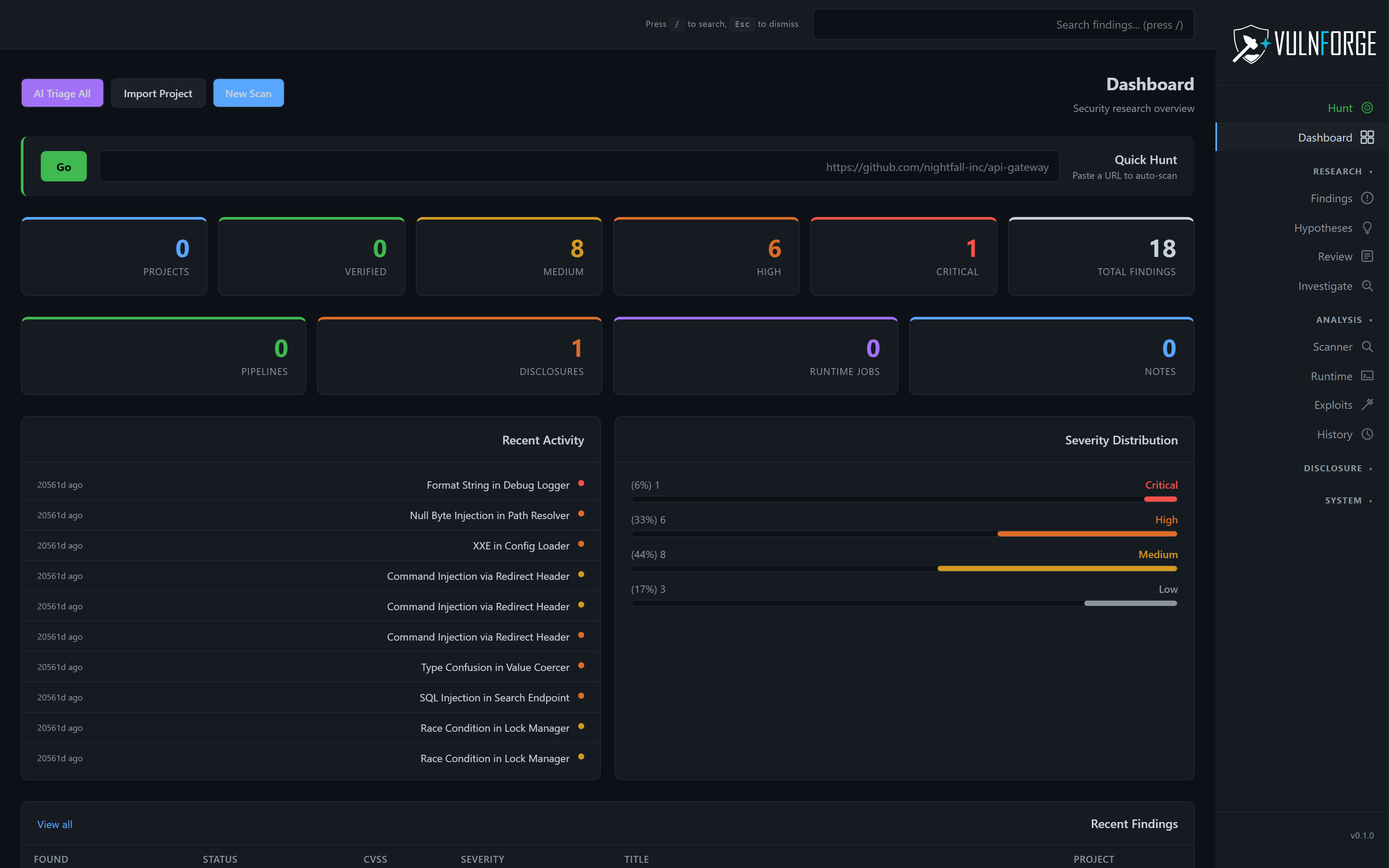
The autonomous pipeline handles the entire lifecycle. Clone, analyze, scan, filter, verify, and stage findings for review — all from one Git URL or local path. Pause mid-pipeline and resume later. Batch mode scans multiple targets in parallel. No-AI mode works out of the box.
- Paste-a-URL hunts — auto-detect language and pick the right tools
- Pause / resume — long-running jobs survive restarts
- Batch mode — parallel multi-target
- No-AI mode — add providers later